Introduction
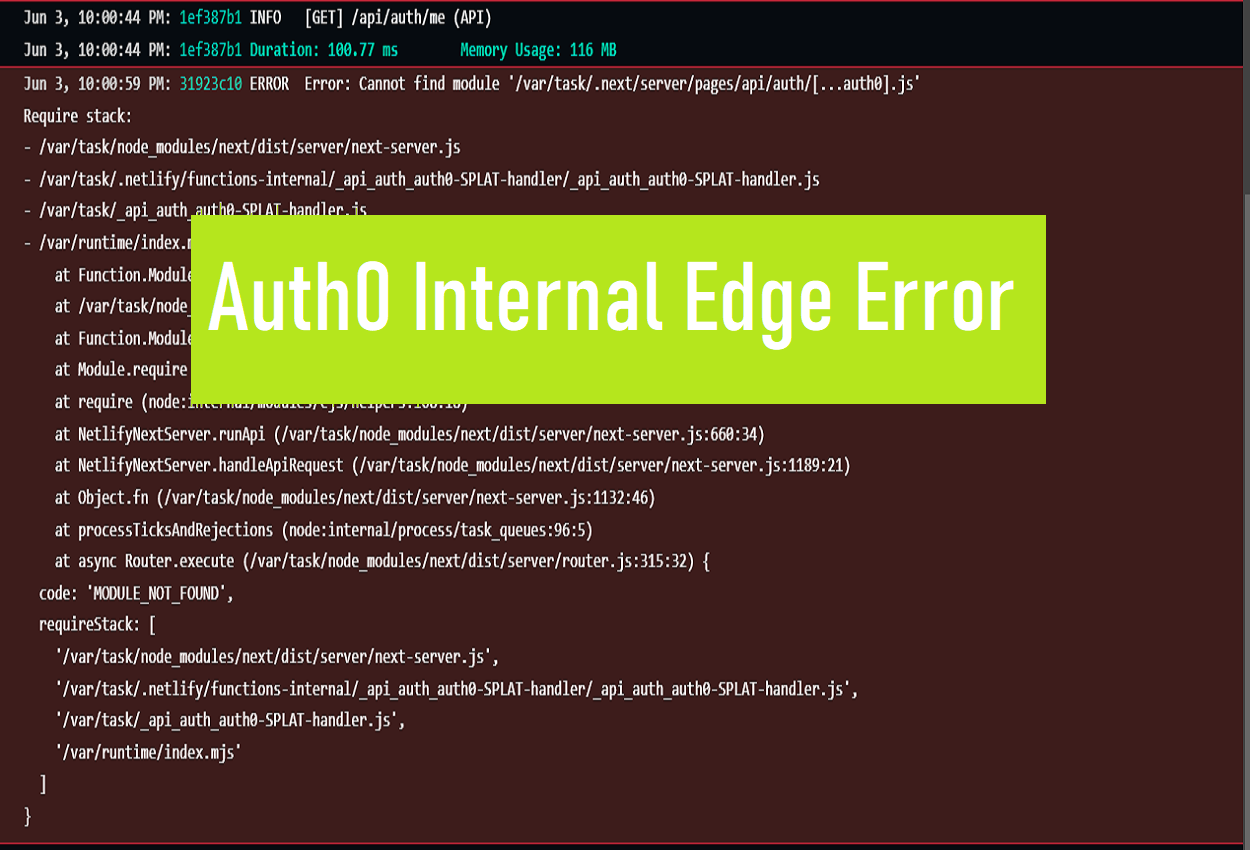
When using Auth0 for authentication and authorization in your applications, you may occasionally encounter an ” Auth0 Internal Edge Error.” This error prevents users from logging in or accessing protected resources, so resolving it quickly is important to maintain availability of your app.
Recent Released: Surf Smart: Your Internet Plan Guide
In this comprehensive guide, we’ll cover common causes of the Auth0 Internal Edge Error, steps to troubleshoot the issue, and methods to prevent it from occurring. By the end, you’ll be equipped with the knowledge to diagnose and fix this error efficiently when it pops up.
What Causes the Auth0 Internal Edge Error?
There are a few potential reasons you may see an Internal Edge Error from Auth0. Here are some of the most common causes:
1. Problem with Retrieving Public Keys for JWT Validation
One source of this error is Auth0 returning a 503 status code with an “Internal Edge Error” message instead of returning the public keys needed to validate a JWT (JSON Web Token).
Public keys are required to verify the signature of a JWT. If the keys can’t be retrieved from Auth0, the JWT can’t be validated, resulting in the edge error.
2. Incorrect DNS Configuration for Custom Domain
If you use a custom domain with Auth0, the DNS settings need to be configured properly to route traffic correctly. If these settings are incorrect, it can lead to edge errors when trying to reach Auth0 endpoints.
Double check that your DNS contains the correct CNAME record pointing your custom domain to the appropriate Auth0 domain.
3. Conflict Between User Accounts with Same Username
The Auth0 Internal Edge Error may appear when attempting to change a user’s password if there is a conflict between two user accounts sharing the same username.
For example, if a user profile created through a database connection has the same username as a user from a social identity provider, it can create a conflict and lead to an edge error.
4. Pre-Registration Flow Overwriting user_id
In some cases, the Pre-Registration flow in Auth0 can add a user_id to the app_metadata field, overwriting the actual unique user_id. This leads to mismatches between user accounts that prevent login.
Check your app_metadata fields after using Pre-Registration to ensure the user_id hasn’t erroneously been overwritten.
5. Browser Exceptions When Accessing localStorage
Some browsers, like new versions of Microsoft Edge, can throw exceptions when JavaScript code tries to access window.localStorage. Because Auth0 utilizes localStorage, this browser behavior can lead to edge errors.
Try testing in different browsers to see if one exhibits the issue versus another.
6. Internet Explorer / Edge Issues Accessing Auth0 Domain
Some users have reported issues with IE and Edge failing to access their Auth0 domain and profile pages, with errors like INET_E_DOWNLOAD_FAILURE or INET_E_INVALID_URL. This prevents loading the necessary resources for authentication.
If you encounter these specific errors, check that the URLs are formatted correctly and that the same access issues do not occur in other browsers like Chrome or Firefox.
How to Troubleshoot the Auth0 Internal Edge Error
When this error appears, there are a number of troubleshooting steps you can take to get to the bottom of it:
1. Check the Auth0 Status Page
First, check the Auth0 status page to see if there are any ongoing issues, incidents, or maintenance that could be related. This can give insight into whether the problem is specific to your app or affecting the Auth0 platform as a whole.
2. Clear Browser Cache and Cookies
A quick first step is to clear your browser cache and cookies for the site in question, then try to log in again. This will remove any corrupted tokens or artifacts that could be causing problems.
In Chrome, you can do this by going to Settings > Privacy and Security > Cookies and other site data > Clear data.
3. Verify Correct DNS Configuration for Custom Domain
If you are using a custom domain, double check that the DNS configuration contains a valid CNAME record mapping your domain to an Auth0 domain, e.g:
Copy code
custom-domain.com CNAME tenant.auth0.comIncorrectly configured DNS is a common source of edge errors.
4. Check Application Logs for Error Details
Your app logs may contain additional error messages and details that are not shown in the browser. Inspect the logs during a failed login to see if there are any references to the edge error or other related issues.
Logs with an “UnsupportedGrantType” error, for example, can indicate a problem with the OAuth authorization grant.
5. Look for Conflicting User Accounts with Same Username
Scan your user directory connections to see if there are two accounts with identical usernames. As mentioned previously, a conflict here can lead to edge errors on login and when changing passwords.
Check database connections as well as any social or enterprise identity provider connections.
6. Verify User Identifier in App Metadata
If you utilize the Pre-Registration feature, check that it is not erroneously overwriting the unique user_id field in app_metadata.
This should contain a random unique identifier, not profile attributes like email or username.
7. Try Alternative Browsers
Some browsers may exhibit problems in specific scenarios, like IE and Edge with localStorage usage. Testing in an alternative browser can help isolate whether the issue is specific to a certain browser.
If Chrome or Firefox work successfully, it points to a browser-specific problem versus an overall configuration issue.
8. Contact Auth0 Support
If you continue encountering the internal edge error after exhausting other troubleshooting methods, reach out to Auth0 support.
They can investigate further by examining your Auth0 tenant configuration, logs, and any other environmental factors that could be contributing to the problem.
Preventing Auth0 Internal Edge Errors
Once you resolve an internal edge error, you can take proactive measures to prevent it from cropping up again in the future:
Cache Public Keys Locally for JWT Validation
To avoid errors from failed retrieval of public keys from Auth0, cache them locally and only fetch updated keys when they expire or are rotated.
This guarantees you have valid keys for token validation.
Automate DNS Configuration Checks
Set up a scheduled script or monitoring system to automatically check for DNS issues with your custom domain to catch problems proactively before they impact users.
Provision User Accounts Carefully
When provisioning new user accounts, take care to avoid duplicate usernames across account types that could lead to conflicts.
Audit existing accounts periodically to check for collisions as your userbase grows.
Perform Load Testing
Conduct load testing regularly to verify your apps and infrastructure can handle peak traffic levels without edge errors emerging under high load.
This helps identify capacity issues before they interrupt regular usage.
Auth0 Internal Edge Error Troubleshooting Checklist
To summarize the troubleshooting process for an Auth0 Internal Edge Error:
- Check Auth0 Status page for known issues
- Clear browser cache and cookies
- Confirm custom domain DNS configuration is correct
- Review application logs for additional error details
- Look for conflicting user accounts with the same username
- Verify user_id field in app_metadata
- Try alternative browsers like Chrome or Firefox
- Contact Auth0 support if issue persists
Following these steps will help diagnose the underlying cause so you can get back to normal operation as quickly as possible.
Conclusion
Debugging and resolving an Auth0 Internal Edge Error ultimately comes down to methodically eliminating potential causes until the source is identified. Start with the common culprits like DNS configuration and conflicting user accounts.
Check error logs and try different browsers for additional clues, and reach out to Auth0 support if you need assistance. With the right approach, you can diagnose and fix edge errors rapidly.
Implementing proactive measures like local caching of public keys, automated DNS checks, carefully provisioning user accounts, and regular load testing will help minimize future occurrences. Bookmark this guide for a handy troubleshooting reference anytime an Auth0 Internal Edge Error appears!